How Does Apple Generate An Encryption Keys
Feb 18, 2016 The encryption used by the iPhone to protect its storage is a multi-tiered system. At its core are two keys, one embedded in the hardware and the. The certificate, key, and trust services API is a collection of functions and data structures that you use to conduct secure and authenticated data transactions. Specifically, you use this API to manage and use: Certificates and identities. A certificate is a collection of data that identifies its owner in. Jan 16, 2018 Briefly, the Cloud Key Vault uses a specialized piece of hardware called a Hardware Security Module (HSM) to store encryption keys. This HSM is a physical box located on Apple property. Users can access their own keys if and only if they know their iCloud Keychain password — which is typically the same as the PIN/password on your iOS device. Master keys as you hear them used in SSL/TLS or SSH are different. Generally speaking the shared secret with be mixed with a secure algorithm so that both parties can generate a Master Key. The Master Key is then used to generate the Encryption Keys, Integrity Keys.
- How Does Apple Generate An Encryption Keys In Excel
- Does Encryption Make Files Bigger
- How Does Encryption Protect Data
Creating and managing keys is an important part of the cryptographic process. Symmetric algorithms require the creation of a key and an initialization vector (IV). The key must be kept secret from anyone who should not decrypt your data. The IV does not have to be secret, but should be changed for each session. Asymmetric algorithms require the creation of a public key and a private key. Pyhton key generation using aes265 in ctr mode. The public key can be made public to anyone, while the private key must known only by the party who will decrypt the data encrypted with the public key. This section describes how to generate and manage keys for both symmetric and asymmetric algorithms.
Symmetric Keys
The symmetric encryption classes supplied by the .NET Framework require a key and a new initialization vector (IV) to encrypt and decrypt data. Whenever you create a new instance of one of the managed symmetric cryptographic classes using the parameterless constructor, a new key and IV are automatically created. Anyone that you allow to decrypt your data must possess the same key and IV and use the same algorithm. Generally, a new key and IV should be created for every session, and neither the key nor IV should be stored for use in a later session.
To communicate a symmetric key and IV to a remote party, you would usually encrypt the symmetric key by using asymmetric encryption. Sending the key across an insecure network without encrypting it is unsafe, because anyone who intercepts the key and IV can then decrypt your data. For more information about exchanging data by using encryption, see Creating a Cryptographic Scheme.
The following example shows the creation of a new instance of the TripleDESCryptoServiceProvider class that implements the TripleDES algorithm.
When the previous code is executed, a new key and IV are generated and placed in the Key and IV properties, respectively.
Sometimes you might need to generate multiple keys. In this situation, you can create a new instance of a class that implements a symmetric algorithm and then create a new key and IV by calling the GenerateKey and GenerateIV methods. The following code example illustrates how to create new keys and IVs after a new instance of the symmetric cryptographic class has been made.
When the previous code is executed, a key and IV are generated when the new instance of TripleDESCryptoServiceProvider is made. Another key and IV are created when the GenerateKey and GenerateIV methods are called.
Asymmetric Keys
The .NET Framework provides the RSACryptoServiceProvider and DSACryptoServiceProvider classes for asymmetric encryption. These classes create a public/private key pair when you use the parameterless constructor to create a new instance. Asymmetric keys can be either stored for use in multiple sessions or generated for one session only. While the public key can be made generally available, the private key should be closely guarded.
A public/private key pair is generated whenever a new instance of an asymmetric algorithm class is created. After a new instance of the class is created, the key information can be extracted using one of two methods:
The ToXmlString method, which returns an XML representation of the key information.
The ExportParameters method, which returns an RSAParameters structure that holds the key information.
Both methods accept a Boolean value that indicates whether to return only the public key information or to return both the public-key and the private-key information. An RSACryptoServiceProvider class can be initialized to the value of an RSAParameters structure by using the ImportParameters method.
Asymmetric private keys should never be stored verbatim or in plain text on the local computer. If you need to store a private key, you should use a key container. For more on how to store a private key in a key container, see How to: Store Asymmetric Keys in a Key Container.
The following code example creates a new instance of the RSACryptoServiceProvider class, creating a public/private key pair, and saves the public key information to an RSAParameters structure.
See also
Turn on and set up FileVault
FileVault 2 is available in OS X Lion or later. When FileVault is turned on, your Mac always requires that you log in with your account password.
- Choose Apple menu () > System Preferences, then click Security & Privacy.
- Click the FileVault tab.
- Click , then enter an administrator name and password.
- Click Turn On FileVault.
If other users have accounts on your Mac, you might see a message that each user must type in their password before they will be able to unlock the disk. For each user, click the Enable User button and enter the user's password. User accounts that you add after turning on FileVault are automatically enabled.
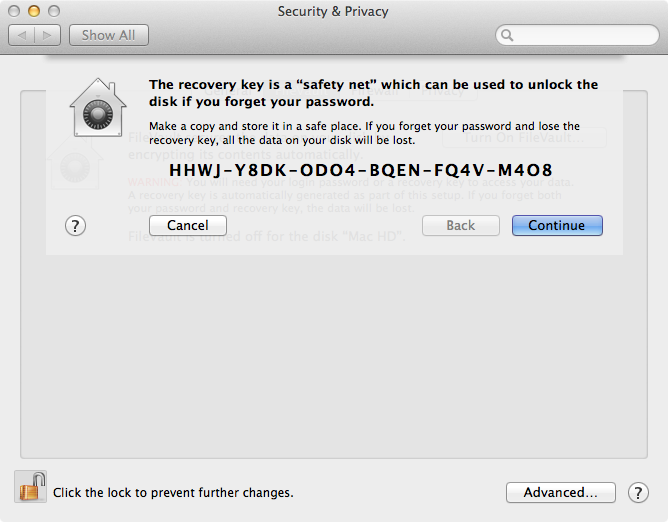
Choose how you want to be able to unlock your disk and reset your password, in case you ever forget your password:
- If you're using OS X Yosemite or later, you can choose to use your iCloud account to unlock your disk and reset your password.*
- If you're using OS X Mavericks, you can choose to store a FileVault recovery key with Apple by providing the questions and answers to three security questions. Choose answers that you're sure to remember.*
- If you don't want to use iCloud FileVault recovery, you can create a local recovery key. Keep the letters and numbers of the key somewhere safe—other than on your encrypted startup disk.
If you lose both your account password and your FileVault recovery key, you won't be able to log in to your Mac or access the data on your startup disk.
Encryption occurs in the background as you use your Mac, and only while your Mac is awake and plugged in to AC power. You can check progress in the FileVault section of Security & Privacy preferences. Any new files that you create are automatically encrypted as they are saved to your startup disk.
When FileVault setup is complete and you restart your Mac, you will use your account password to unlock your disk and allow your Mac to finish starting up. FileVault requires that you log in every time your Mac starts up, and no account is permitted to log in automatically.
How Does Apple Generate An Encryption Keys In Excel
Reset your password or change your FileVault recovery key
If you forget your account password or it doesn't work, you might be able to reset your password.
Does Encryption Make Files Bigger
If you want to change the recovery key used to encrypt your startup disk, turn off FileVault in Security & Privacy preferences. You can then turn it on again to generate a new key and disable all older keys.

Turn off FileVault
If you no longer want to encrypt your startup disk, you can turn off FileVault:
- Choose Apple menu > System Preferences, then click Security & Privacy.
- Click the FileVault tab.
- Click , then enter an administrator name and password.
- Click Turn Off FileVault.
Decryption occurs in the background as you use your Mac, and only while your Mac is awake and plugged in to AC power. You can check progress in the FileVault section of Security & Privacy preferences.
How Does Encryption Protect Data
Learn more
- Learn how to create and deploy a FileVault recovery key for Mac computers in your company, school, or other institution.
- If you're using FileVault in Mac OS X Snow Leopard, you can upgrade to FileVault 2 by upgrading to OS X Lion or later. After upgrading OS X, open FileVault preferences and follow the onscreen instructions to upgrade FileVault.
- RAID partitions or non-standard Boot Camp partitions on the startup drive might prevent OS X from installing a local Recovery System. Without a Recovery System, FileVault won't encrypt your startup drive. Learn more.
* If you store your recovery key with Apple or your iCloud account, there's no guarantee that Apple will be able to give you the key if you lose or forget it. Not all languages and regions are serviced by AppleCare or iCloud, and not all AppleCare-serviced regions offer support in every language. If you set up your Mac for a language that AppleCare doesn't support, then turn on FileVault and store your key with Apple (OS X Mavericks only), your security questions and answers could be in a language that AppleCare doesn't support.



